
Bot® is a reference in professional data recovery in Portugal, Spain and Brazil. We combine security, precision and advanced technology to restore files from hard drives (HDD), SSDs, RAID systems, NAS, servers and mobile devices. We have already solved more than 200,000 real cases, with a 95% success rate and total confidentiality in every process.
Some of our clients:

We recover data from HDDs with logical, mechanical and electronic failures in a controlled cleanroom environment (WhiteRoom®), using certified processes and ensuring complete confidentiality.
Initial Care and Common Questions in HDD Recovery
My HDD is clicking. Can it still be recovered?
Yes, but power it off immediately and never open the drive. Clicking indicates a mechanical failure, and each attempt can make it worse. Request a free evaluation with us and follow the shipping or drop-off instructions.
I accidentally formatted my HDD. Is it possible to recover the data?
In most cases, yes — especially if no new data has been written afterwards. The analysis will confirm feasibility and the best recovery method.
How long will it take and how will I receive my data?
Typically 4–10 days (depending on complexity). Data delivery may be via secure download, USB flash drive or external HDD, depending on the data volume. (See details in our Help Center)

We handle physical failures (drops, impacts), logical failures (deletion/formatting), and cases where the “external hard drive is not recognized.” All procedures are carried out in a certified Class 100 Cleanroom, with strict protocols to protect sensitive data.
Windows asks me to format my external hard drive. Should I accept?
No. Formatting may overwrite metadata and files. Power it off and request a professional evaluation.
Will changing the enclosure fix an “unrecognized disk”?
Rarely. The issue may lie in the internal HDD or controller board. A full laboratory analysis is required.
Can I keep trying different ports/cables?
Avoid it. Repeated attempts may worsen physical or logical damage. Send the device for expert evaluation.

Experts in controllers, mappings, and ECC/WL algorithms. We handle electronic failures, firmware issues, and NAND cell degradation while maintaining full data integrity — always under strict confidentiality.

We handle both logical and physical failures, including direct NAND chip reading when required, controller reconstruction, and full data integrity validation.
Typical Scenarios
The USB drive is burned or the connector is broken. Is recovery still possible?
In many cases, yes, through direct memory reading.
The USB drive is asking to be formatted. Should I proceed?
No. This may cause permanent data loss. Request a diagnosis.
Does the price depend on the amount of data?
No. The cost depends on the complexity, not the data volume (see pricing page and Help Center).

Direct memory extraction (when required), controller interpretation, and logical reconstruction to recover photos, videos, and documents.
I deleted or formatted my card. Can my photos be recovered?
In most cases, yes — provided that no new data has been written over the original files.
The card asks to be formatted. Should I try to “repair” it?
Avoid automated utilities. They can overwrite critical metadata and make recovery impossible.
Will recovered files keep their quality (RAW/4K)?
Yes, as long as the affected sectors haven’t been overwritten. We perform integrity checks on sampled files before every delivery.

Technical response for ransomware infections involving file encryption: specialized diagnostics, immediate containment, and real recovery strategies — without false promises and with precise guidance at every stage.
Do you guarantee decryption of any ransomware?
It’s neither ethical nor realistic to guarantee 100%. We analyze the ransomware variant, extension, and technical possibilities before proposing recovery paths.
Can I use free tools from the internet?
We don’t recommend it. There’s a high risk of permanently corrupting your data. Preserve all evidence and contact the laboratory.
Is it possible to recover affected VMs or backups?
In many cases, yes. Corporate incidents often require a dedicated technical plan and a specialized server recovery lab.

Solutions to recover RAID 0/1/5/6/10/50 and variations: controlled reading, reconstruction of corrupted RAID, parity and metadata handling, consistency validation, and secure data extraction.
The rebuild failed and the volume got worse. Is there still a solution?
In many cases, yes — but each wrong attempt worsens consistency. It is very important to remove the RAID components (HDD or SSD) and stop using them.
Can I replace the controller and try to assemble it again?
There is a high risk of incompatibility and overwriting. The best option is a specialized analysis.
Does the budget depend on the number of drives?
It depends on the complexity (RAID level, drive condition, metadata), not only on the quantity.

Specialized laboratory for configuration failures, controller issues, inaccessible network volumes, missing files from NAS devices, etc. We recover NAS systems such as WD MyCloud, Synology, QNAP, and others with different RAID levels.
The NAS lost its configuration and the volume disappeared. What should I do?
Do not recreate the volume/RAID. This may overwrite the original configuration.
Can I remove and test the drives individually?
Avoid doing so. The order and condition of the drives are essential for reconstruction.
Can you work with any brand/model?
Yes, we work with all major manufacturers and systems.

We recover inaccessible or deleted recordings from various manufacturers and proprietary file systems — including HDDs that “click” or request formatting.
Is it possible to recover deleted videos?
In many cases, yes — depending on overwriting and the DVR system.
The DVR hard drive is defective. Is there still a chance?
Yes, we repair the hard drive issues and extract the footage using proprietary methods.
Do you work with proprietary formats?
Yes. We support dozens of manufacturers and systems.

We work on damaged devices (won’t power on, boot loop, burnt or broken) using advanced memory reading and extraction techniques.
The device does not turn on or is stuck in a boot loop. Is recovery still possible?
In many cases, yes, with controlled extraction. Cases involving factory reset contain no recoverable data.
Can you recover deleted WhatsApp messages?
No.
The device got wet. Can I try to dry it and turn it on?
Avoid turning it on — oxidation progresses. Request a diagnosis and follow a specialist’s instructions.

Recovery for MacBooks, iMacs, Mac mini/Pro, and devices with soldered SSDs (post-2016), using component transfer processes and secure data reading methods.
MacBook with a soldered SSD: is it possible to recover?
Yes, through bench-level procedures and the use of appropriate tools.
Does the T2 chip prevent recovery?
It increases the complexity, but we evaluate possible solutions case by case.
Can I use “Internet Recovery” and reinstall macOS?
Avoid doing so, as it may overwrite data. Prioritize diagnostic analysis first.
Bot readings and pages
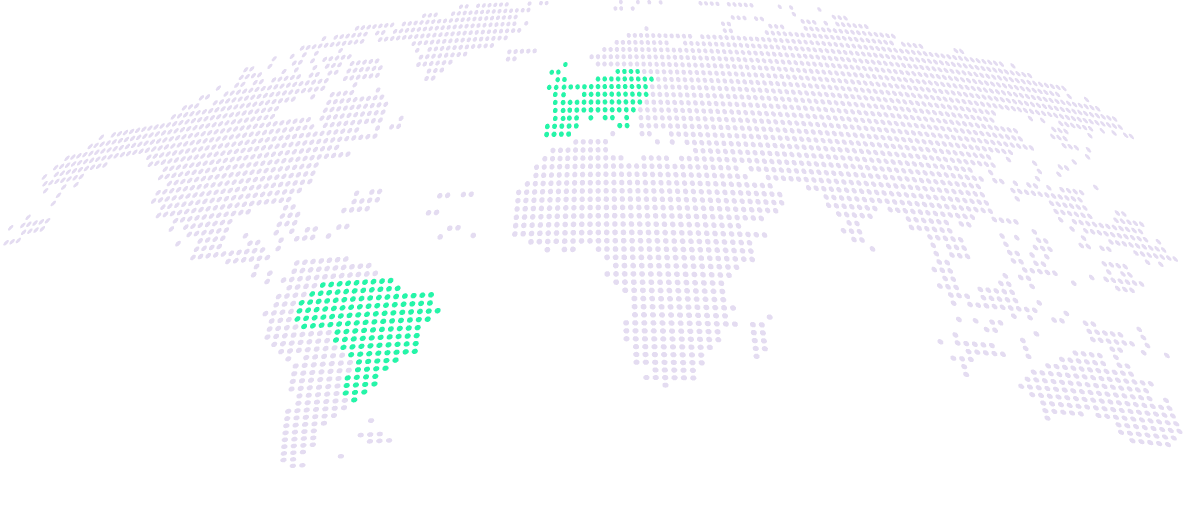
Bot® operates across Brazil, Portugal, and Spain, providing specialized, fast, and secure data recovery services in major cities. Our laboratories follow the same international standards of quality, confidentiality, and precision — wherever you are.
1
2
3
4
We deliver the recovered data on an external drive with encryption enabled. Our laboratories have restricted access and follow strict confidentiality protocols.
The data recovery industry still faces practices that can mislead clients, such as forged reviews and lack of clarity in information. To change this, we created an exclusive movement for transparency and trust, helping you choose safely before deciding on a laboratory.
Avoid fake reviews and learn about our reputation.
There are three types of budgets: normal (48h), priority (24h), or urgency (12h). Recovery with an emergency team available 24/7/365.
We offer a free quotation and even free shipping of your device for analysis
Encryption technologies ensure your data never circulates without protection.
We deliver your recovered data free of charge — clean, organised and ready to use — to ensure you have a great experience!
Full compliance with data protection laws (LGPD/GDPR) and adherence to international standards of quality, privacy and security.
What do our clients say?
I thought I had lost years of work when my hard drive stopped working. In other repair centres, I was told it was a total loss. At Bot, from the very first contact, I felt a sense of security and clarity. The team explained the entire process, kept me informed at every stage, and in the end, they returned almost all of my files. It’s not just about technology — it’s about trust and professionalism. I recommend them with complete confidence.
Guilherme Heck
Carolina Félix
Thiago Dias
A trustworthy company with clear communication and outstanding results. They recovered more than 1 TB of files I had already considered lost. Forever grateful.
Fernanda Cohen

Rodrigo Nunes

Patrícia Gomes
3 tips to increase the chances of successful data recovery
Power off
Unusual noises
Deleted or formatted files
The price depends on the type of failure and the technical complexity. For transparency, we publish starting prices on our data recovery pricing page.